
Secure Entry
Identify authorized users and provide them fast, frictionless entry.
Ideal for: hotels (for registration, room entry, etc.), office buildings, residential buildings, hospitals, schools, and gyms.
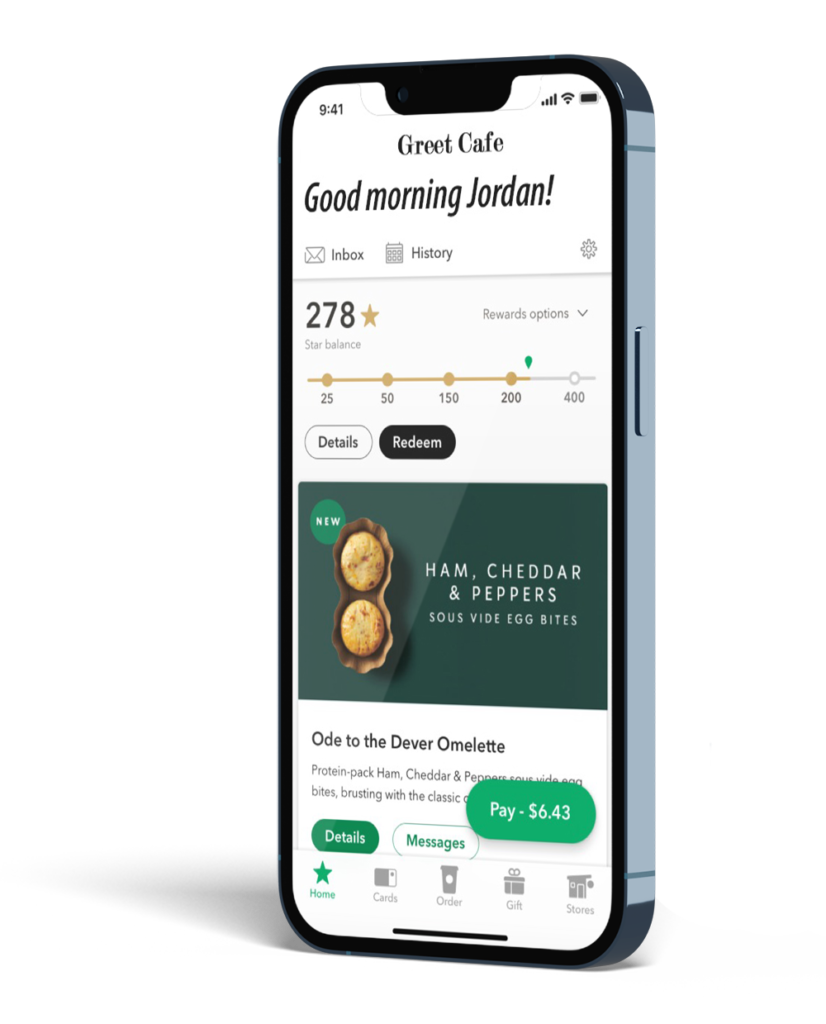
Pre-Ordering
Reach out to approaching customers via text or app to take orders before arrival to speed up pick-up and make your staff more efficient.
Ideal for: take-out restaurants, pharmacies, supermarket delis, bakeries and fish and meat counters.
Welcoming Customers by Name
Business representatives can receive alerts when customers are arriving in order to offer enhanced, VIP services such as greeting the customers by name and providing a more customized experience.
Ideal for: Banks, retail, hotels, and gyms.
Real-time Promotion
Send either general or personalized promotions tailored to each customer as they approach, enter and move around the premises.
Ideal for: Retailers of all kinds, including supermarkets and restaurants.
Behavioral Tracking
Track the arrival/departure time and movement of Customers, Employees, Vendors, etc. to optimize operations and staffing.
Valuable for all industries.
Two Business Problems
Problem 1: Businesses are unable to influence their customers’ purchases or user experience as they arrive, enter and move within, because they are unable to recognize these customers and unable to send them real-time texts and messages. These businesses would like to be able to communicate at the right time and place with targeted messages.
Problem 2: For businesses with a mobile app, the mobile app is rarely open on customers’ phones, making it impossible to push messages to customers through the business’s mobile app.
Two Solutions
Greet boasts unique, patented features which enable Greet businesses to solve the problem of recognizing and sending real-time messages to registered customers. Greet can also automatically open the business’s mobile app on customer phones, thereby dramatically boosting customer use of the business’s app.
Business Use of Greet Solutions
Businesses can use Greet to monitor the arrival and movement of registered and unregistered customers, employees and vendors. As these different users arrive and move about the premises, Greet can be easily configured to trigger automatic text or in-app messages to customers, employees and managers.
Greet can enhance the customer experience on many levels, through a range of use cases:
Identifying customers is done in a broad variety of ways, each of which has strengths and weaknesses. Conceptually these fall into three categories:
Who You Are
Human beings are unique. Our unique genetic makeup expresses itself in multiple ways including facial features and iris features, finger and palm prints. Other features such as gait and speech fall into the category of ‘Who you are”. In order to use such features to identify individuals there is typically a process whereby the subject registers their biometrics and then each time they arrive at a destination goes through a scanning process to confirm that their characteristics match the stored characteristics. This process provides great accuracy but has the following negatives:
What You Know
What You Know refers mainly to passwords. The advantage of passwords is that, unlike biometrics, they are changeable, which mitigates damage. Unfortunately human behavior undermines passwords. People tend to use passwords that are easily remembered and therefore easily hacked. They tend to use the same password in different sites and they are easy prey for fraudulent phishing schemes.
What You Have
Physical objects carried by users is the final category. Physical and electronic keys, tokens, data cards, and cell phones fall into this category.
The advantage of physical objects for authentication is that theft must either rely upon obtaining the object (e.g. a security ID) or replicating it.
Authentication through physical devices has the following negatives:
In the category of What You Have, cell phones have the following advantages:
What is Greet’s core and differentiated functionality?
Greet is an innovative technology and white-label product that your business can use to identify individuals and send personalized or general texts or in-app messages to your customers and employees as they arrive and move within your locations, without them having to open your app.
Greet is the only non-GPS solution able to recognize the customer and send them texts or in-app messages based on their location near or within your premises.
Is Greet useful for my particular business?
If your business has physical locations regularly visited by customers, employees, tenants, vendors, etc. then Greet’s functionality will fit your business needs.
How can I send in-app messages to arriving customers if they do not have my app open?
Whenever the customer’s phone is detected on or near the premises, Greet automatically opens your mobile app on each customer’s phone– as if the user had stopped and manually opened the app themselves– enabling you to send in-app messages to the arriving customer.
Is there another technology out there that opens my business’s mobile app on my customers’ phones?
No. Automatically opening the mobile app on users’ phones is proprietary to Greet and is patent-protected.
How will automatically opening my mobile app on my users’ phones affect user usage of our mobile app?
The average user has more than 60 apps on their phone with only three or fewer open at a time. On-location mobile app use by users is typically low, often less than 10%. On-location automatic app opening will cause on-site app use to rise dramatically (100% of registered users). Once your app opens on users’ phones, you can automatically communicate with those users (e.g., customers/employees/business reps and execs) as they arrive and as they move within the premises of your locations.
Does my business need a mobile app to take advantage of Greet’s functionality?
If you have a mobile app to which you’d like to add Greet’s functionality, integrating Greet’s SDK with your existing technology stack is simple and the Greet team can do this if your IT team is busy. Greet has created SDKs for iOS, Android and hybrid platforms.
If you don’t have a mobile app or would rather not use it for this purpose, Greet can create a mobile app for you that leverages all its functionality.
Finally, if you don’t want to communicate with your customers (or employees, vendors, or tenants) through an app, then Greet will allow you to do so via text message. User registration would then be done on the business’ website site. Greet can do this simple development for you.
How is Greet’s location-recognition/tracking technology different or better than GPS and others?
Greet uses Wi-Fi and Bluetooth technologies which only track a user when they are very close to the Wi-Fi scanner or Bluetooth device (aka beacon).
Most location-tracking apps use GPS geofencing which tracks a user’s location everywhere they go. When people sign up for the location-linked services they are given the option of declining to be tracked, agreeing to be tracked all the time, or agreeing to be tracked only when they have the mobile app open. Invariably they choose the third of these options because they are concerned about being tracked everywhere they go, all the time, as well as about draining battery life.
Greet solves the customer’s/ user’s privacy concern of being tracked everywhere since the tracking only happens at the site of the scanner/beacon, causing opt-in to location-based communication to dramatically increase.
From the customer’s point of view, how will things change?
Customers can now be greeted personally and receive useful location-based information such as personalized promotions and services tailored to their needs, as they arrive and as they move within your premises– when you can influence the user’s behavior. In contrast, the existing process of a business knowing who the customer is only when they are paying and leaving is too late to influence their purchase behavior. With Greet, customers can also find and order what they want to buy more quickly and easily.
How exactly do I offer the personalized messaging service to my customers?
You will send a message to your users offering to let them sign up to receive on-site promotions, pre-order notifications and other personalized services relevant to your business. You may choose to offer an incentive for sign-up.
What is the process for customers to sign up for the service?
Registration takes less than 30 seconds and can take place remotely on your mobile app or via web signup or onsite by scanning a QR code.
Can users choose between receiving real-time text messages or mobile app messages?
Yes.
Can my customers control when and where they receive messages?
Yes, at registration you can empower your customers to customize their experience. For example, a customer may only want to receive messages from one of your business’s locations (e.g., their preferred supermarket, café, or health club) or to receive messages only on certain days at specific times.
What about my customers who do not want to be detected and do not want to receive messages?
Customer recognition and messaging is an ‘opt-in’ service, and customers can opt-out at any time. The only users who will ever receive messages from you are those who have registered to receive such messages.
How can I assess the likelihood of customers wanting this service and opting in?
Besides improving the user or customer experience, how can Greet benefit my business? How will I measure its ROI?
What are other ways businesses such as mine can use Greet’s technology?
My IT department is busy. What is involved with implementation?
Greet can provide a complete mobile app solution or Greet functionality can be easily integrated into your mobile app by adding Greet’s SDK (software development kit) to your business’s existing application. Setup is straightforward and can be done by Greet or by your IT team with support from Greet’s implementation team. You can request technical information here.
Is on-site router or beacon installation required?
Businesses can use their existing Wi-Fi network at their sites. For businesses that lack onsite Wi-Fi or want to offer customer messaging separately, Greet’s tech team (or your IT team, if you prefer) installs a Wi-Fi scanner and, if you are also text messaging within the premises, Bluetooth beacons.
Does my team need to set up its own Data Analytics?
Greet Analytics can create analytics dashboards and capabilities on your behalf if desired.
What about the security of customer information?
The architecture of Greet’s solution leaves all your customer information behind your firewall. Your customer information will not be collected at any time by Greet.
Describe the data flow that enables the business to recognize its customers
Greet places scanners at select points outside and within the location and can also place beacons within the premises. As registered customers approach, Greet’s scanner detects the phones of users and passes information identifying the phone to your business’s chosen platform (ie; servers in their data center or their cloud platform). Information passed is encoded so no Personally Identifiable Information (PII) is involved.
The phone’s identifying information is matched against a database of your users (customers, employees, or vendors) within your chosen platform. Your business will then use the rules it has set up to automatically ‘greet’ the user with user-targeted messaging such as greetings, pre-ordering, personalized promotions, or to enable secure entry.
How is the privacy of the customer, employee, or vendor protected?
Since Greet’s use of Wifi and Bluetooth only detects a user’s location when they are in close proximity to your business location, and only if they’ve opted in, users’ locations remain completely un-tracked everywhere else, unlike GPS-driven technology.
Greet identifies only the assigned code of the user’s phone upon detection and will not know the actual user identity or phone number. In this way, the ability Greet grants to businesses to recognize individuals maintains users’ privacy, non-invasively, unlike alternative ways of recognizing individuals like biometrics that recognize facial and other physical characteristics and are rife with issues like false positives, racial bias, and security and are subject to increasing regulations limiting its use.
What is Greet’s pricing model?
Greet’s hardware/software solution is typically licensed to businesses based on the number of scanners and beacons at each location. Alternative licenses based on usage are also available. Request pricing for your use case here.
Who at my organization should evaluate Greet?
Greet is primarily a user experience-enhancing tool for businesses. Marketing, Sales, and Customer Experience executives should be the first to evaluate Greet. Once your business has determined that Greet can improve your customer experience, executives from IT and cybersecurity should evaluate Greet to address concerns regarding privacy, security, implementation, and support.


